So, yeah recent events at a customer lead me to writing this article for my own purposes of documenting what I did and sharing this with you to prevent the frustration I’ve encountered.
Lets just say Adobe isn’t that keen on using its software in a SBC environment or VDI infrastructure. Or you might say they still have the perception of the traditional stand alone work-space. -This is just my opinion
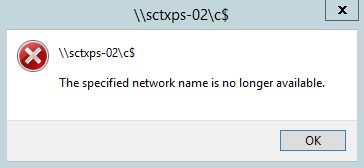
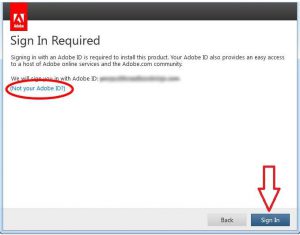
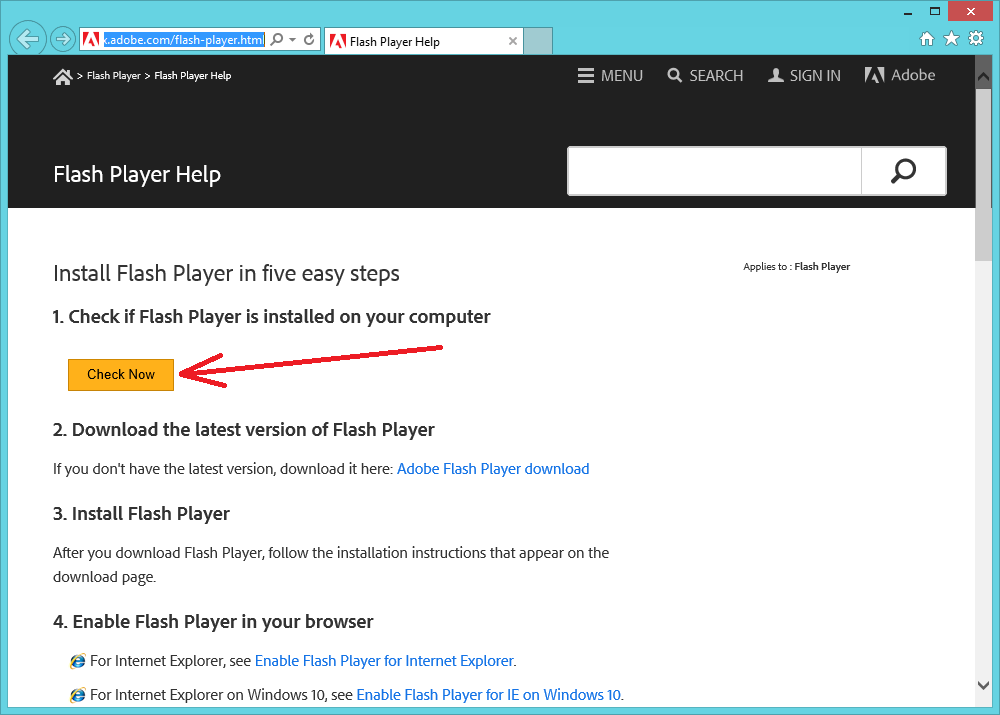
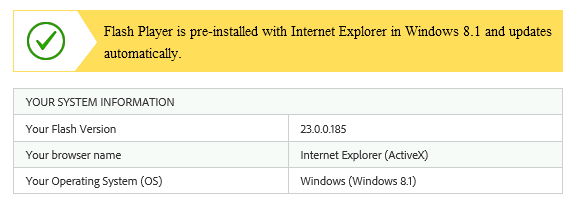
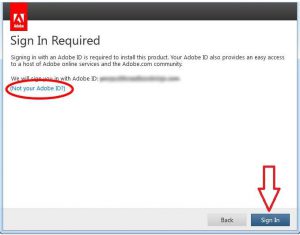
Using a product such as Adobe Acrobat DC requires activation for every single user that uses it, perhaps you have encountered it before. Upon starting Adobe Acrobat, the program closes itself and you are prompted with the following screen:
This to me is just unfeasible in a SBC or non-persistent environment, I guess that’s why this application gets packaged into a Microsoft App-V or VMware thinapp so often.
But since we haven’t got these tools to our possession we needed a different solution. This solution can be found by using adobe_prtk.exe which is part of the Adobe Provisioning Toolkit.
First of all we discovered the customer had a single user license, which will get you nowhere if you want to activate the product for multiple users. Adobe is software that cannot be easily fooled around with (which is a good thing from a anti-piracy standpoint).
So after a quick chat with Adobe support and the software distributor, the client purchased a volume license based on the English language (since this was cheaper).
Now we where able to activate and stream the license (that’s the way Adobe works) to the machines. To do this we will need the following things:
- The serial number
- Grant an offline exception for the product through the Adobe Customization Wizard
- Know if the product is Continues Track or Classic Track (see here)
- License ID or LEID (see here)
- The command lines
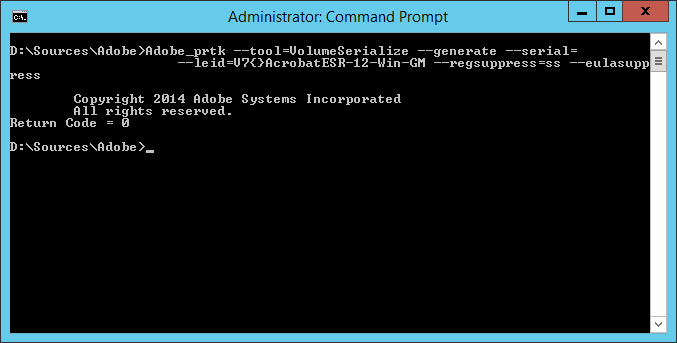
As I said before you’ll need a volume license serial number, the track the customer had or used was “Continuous” and the accompanying “LEID” is: “V7{}AcrobatESR-12-Win-GM”
This leads to the following command line for Adobe_PRTK.exe: “Adobe_prtk –tool=VolumeSerialize –generate –serial=XXXX-XXXX-XXXX-XXXX-XXXX-XXXX –leid=V7{}AcrobatESR-12-Win-GM –regsuppress=ss –eulasuppress”
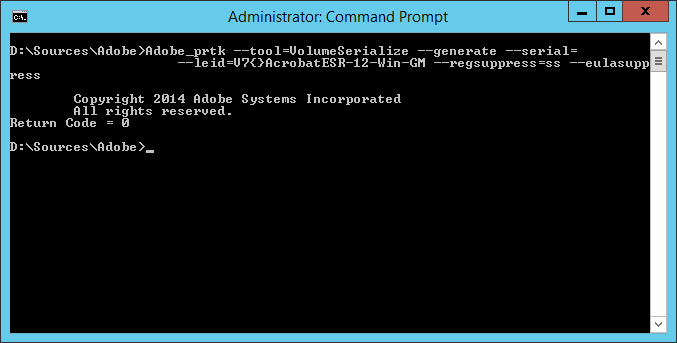
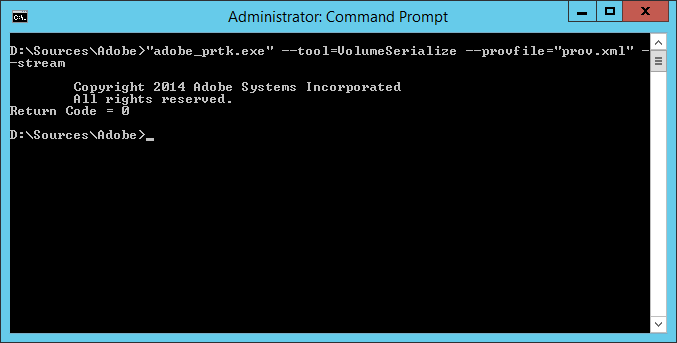
As you can see, the Return Code is “0”, which is a good thing. After running the command above a prov.xml is generated. This file holds the license information. This “prov.xml” file on it’s turn can be used to stream the activation of Adobe Acrobat against machines that are non-persistent such as a VDI work-space, Citrix XenApp MCS or PVS etc.
The command line to use the prov.xml is: adobe_prtk.exe” –tool=VolumeSerialize –provfile=”prov.xml” –stream
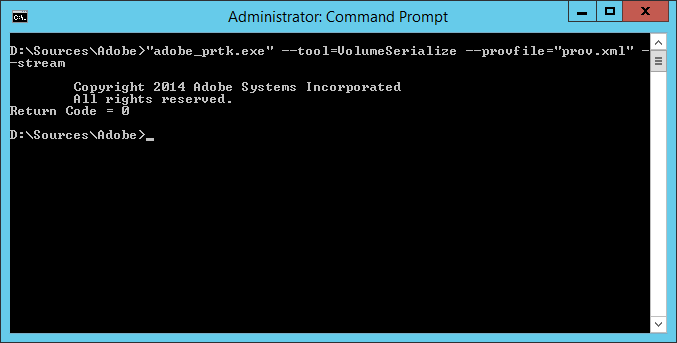
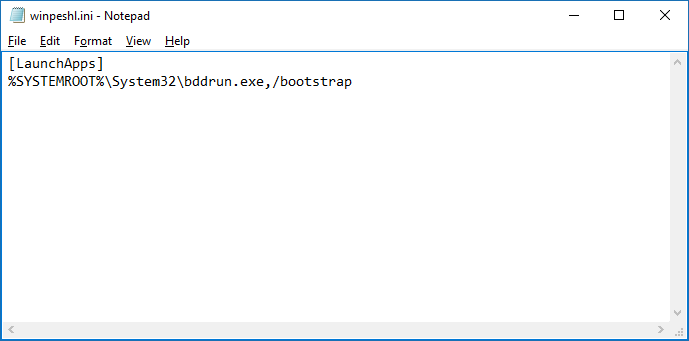
Again if everything is successful the Return Code will be “0”. We have created a job that after every boot or reboot the command line above is executed against every machine Adobe Acrobat is installed on.
This will resolve the “sign-in required” screen in your user sessions. The activation is machine based, however make sure people cannot start Adobe Acrobat more times then you have licenses for.
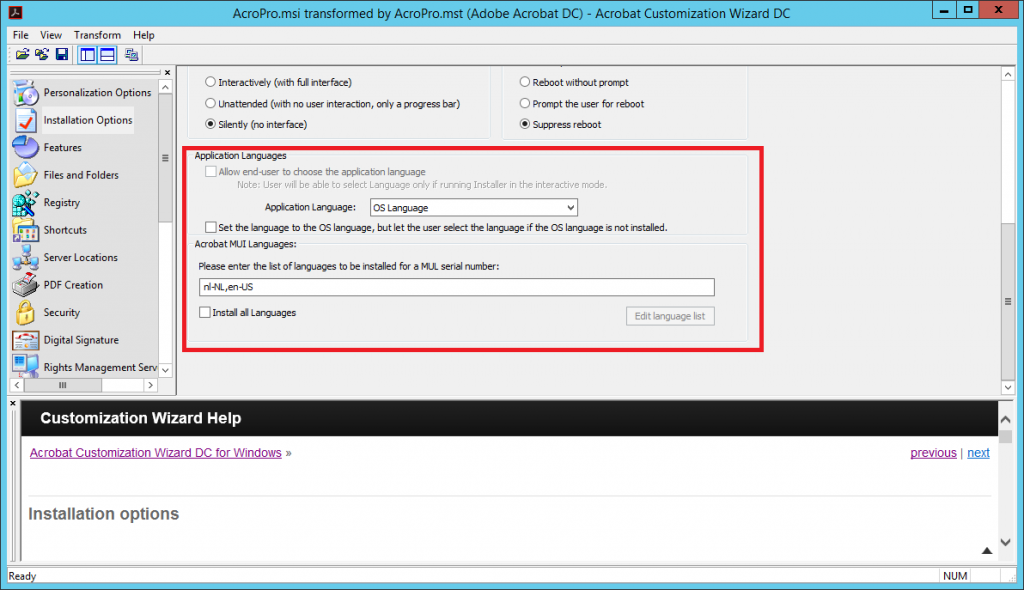
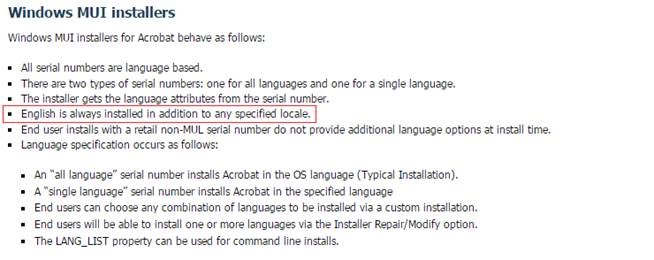
This situation resolved the activation issues with the customer. However there was one oddity happening which we have recently discovered. If you have supplied alternative languages in the Adobe Acrobat Customization Wizard DC, you will need to provide and purchase a license in the desired language. So if you want to have a Dutch Acrobat installation, purchase a Dutch license (licenses in other languages appear to be more expensive then native English).
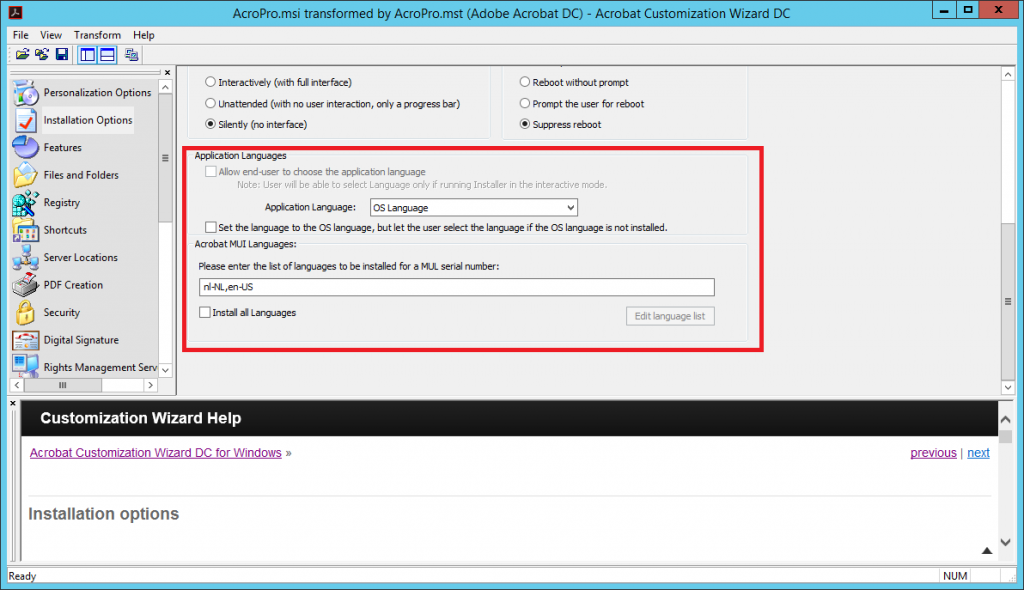
Our software distributor provided a English license because this was cheaper for the client, but when the client switched the desktop from English to Dutch, Adobe needed activation again, the currently streamed license was insufficient and the “Sign-in” required screen prompted again. To avoid this make sure you will only install the English language.
After returning the question to the software distributor the feedback was as following:
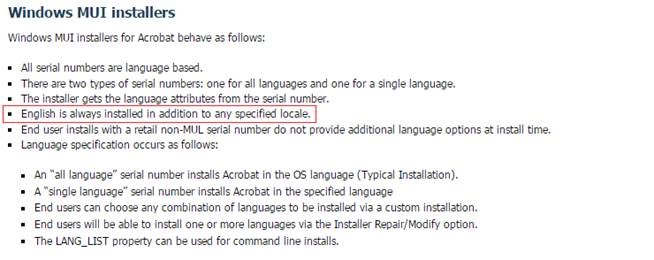
Purchase the language you desire and English is always available, purchase a English only license and no other language can or may be selected.
Hope you find this useful and it will save you time and energy.
– Something wrong? Did I mess up, talking BS or got another trick up your sleeve? Please let me know in the comment section!
Cheers! Rens